Imagine a world where smartphones, laptops, wearables, and other electronics are powered without batteries. Researchers from MIT and elsewhere have taken a step in that direction, with the first fully flexible device that can convert energy from Wi-Fi signals into electricity that could power electronics.
Devices that convert AC electromagnetic waves into DC electricity are known as “rectennas.” The researchers demonstrate a new kind of rectenna, described in a study appearing in Nature, that uses a flexible radio-frequency (RF) antenna that captures electromagnetic waves — including those carrying Wi-Fi — as AC waveforms.
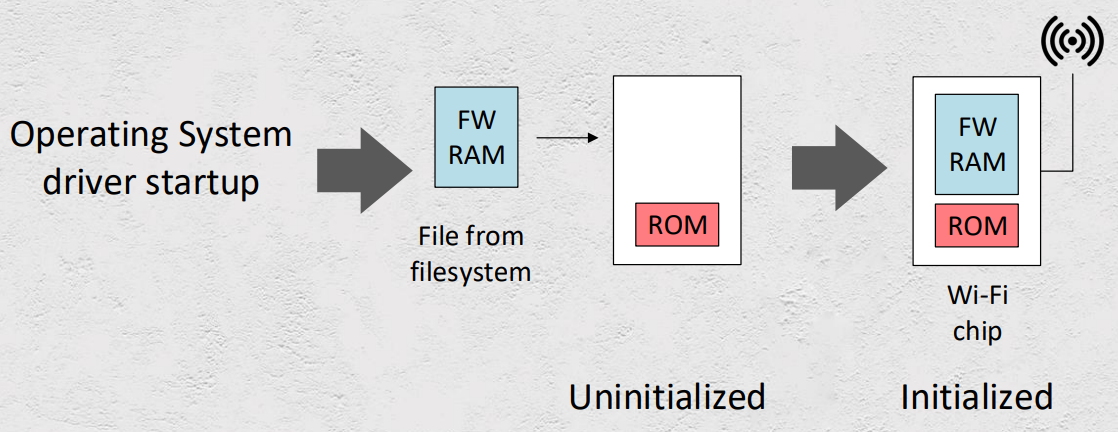
The antenna is then connected to a novel device made out of a two-dimensional semiconductor just a few atoms thick. The AC signal travels into the semiconductor, which converts it into a DC voltage that could be used to power electronic circuits or recharge batteries.
In this way, the battery-free device passively captures and transforms ubiquitous Wi-Fi signals into useful DC power. Moreover, the device is flexible and can be fabricated in a roll-to-roll process to cover very large areas.
“What if we could develop electronic systems that we wrap around a bridge or cover an entire highway, or the walls of our office and bring electronic intelligence to everything around us? How do you provide energy for those electronics?” says paper co-author Tomás Palacios, a professor in the Department of Electrical Engineering and Computer Science and director of the MIT/MTL Center for Graphene Devices and 2D Systems in the Microsystems Technology Laboratories. “We have come up with a new way to power the electronics systems of the future — by harvesting Wi-Fi energy in a way that’s easily integrated in large areas — to bring intelligence to every object around us.”
Promising early applications for the proposed rectenna include powering flexible and wearable electronics, medical devices, and sensors for the “internet of things.” Flexible smartphones, for instance, are a hot new market for major tech firms. In experiments, the researchers’ device can produce about 40 microwatts of power when exposed to the typical power levels of Wi-Fi signals (around 150 microwatts). That’s more than enough power to light up a simple mobile display or silicon chips.
Another possible application is powering the data communications of implantable medical devices, says co-author Jesús Grajal, a researcher at the Technical University of Madrid. For example, researchers are beginning to develop pills that can be swallowed by patients and stream health data back to a computer for diagnostics.
“Ideally you don’t want to use batteries to power these systems, because if they leak lithium, the patient could die,” Grajal says. “It is much better to harvest energy from the environment to power up these small labs inside the body and communicate data to external computers.”
All rectennas rely on a component known as a “rectifier,” which converts the AC input signal into DC power. Traditional rectennas use either silicon or gallium arsenide for the rectifier. These materials can cover the Wi-Fi band, but they are rigid. And, although using these materials to fabricate small devices is relatively inexpensive, using them to cover vast areas, such as the surfaces of buildings and walls, would be cost-prohibitive. Researchers have been trying to fix these problems for a long time. But the few flexible rectennas reported so far operate at low frequencies and can’t capture and convert signals in gigahertz frequencies, where most of the relevant cell phone and Wi-Fi signals are.
To build their rectifier, the researchers used a novel 2-D material called molybdenum disulfide (MoS2), which at three atoms thick is one of the thinnest semiconductors in the world. In doing so, the team leveraged a singular behavior of MoS2: When exposed to certain chemicals, the material’s atoms rearrange in a way that acts like a switch, forcing a phase transition from a semiconductor to a metallic material. This structure is known as a Schottky diode, which is the junction of a semiconductor with a metal.
“By engineering MoS2 into a 2-D semiconducting-metallic phase junction, we built an atomically thin, ultrafast Schottky diode that simultaneously minimizes the series resistance and parasitic capacitance,” says first author and EECS postdoc Xu Zhang, who will soon join Carnegie Mellon University as an assistant professor.
Parasitic capacitance is an unavoidable situation in electronics where certain materials store a little electrical charge, which slows down the circuit. Lower capacitance, therefore, means increased rectifier speeds and higher operating frequencies. The parasitic capacitance of the researchers’ Schottky diode is an order of magnitude smaller than today’s state-of-the-art flexible rectifiers, so it is much faster at signal conversion and allows it to capture and convert up to 10 gigahertz of wireless signals.
“Such a design has allowed a fully flexible device that is fast enough to cover most of the radio-frequency bands used by our daily electronics, including Wi-Fi, Bluetooth, cellular LTE, and many others,” Zhang says.
The reported work provides blueprints for other flexible Wi-Fi-to-electricity devices with substantial output and efficiency. The maximum output efficiency for the current device stands at 40 percent, depending on the input power of the Wi-Fi input. At the typical Wi-Fi power level, the power efficiency of the MoS2 rectifier is about 30 percent. For reference, today’s best silicon and gallium arsenide rectennas made from rigid, more expensive silicon or gallium arsenide achieve around 50 to 60 percent.
There are 15 other paper co-authors from MIT, Technical University of Madrid, the Army Research Laboratory, Charles III University of Madrid, Boston University, and the University of Southern California.
The team is now planning to build more complex systems and improve efficiency. The work was made possible, in part, by a collaboration with the Technical University of Madrid through the MIT International Science and Technology Initiatives (MISTI). It was also partially supported by the Institute for Soldier Nanotechnologies, the Army Research Laboratory, the National Science Foundation’s Center for Integrated Quantum Materials, and the Air Force Office of Scientific Research.